Administrator Guide
This section covers advanced system administration functions available to Manager-level users. These tools are for system configuration, user management, and maintaining the overall health of your AllanaCrusis installation.
Table of contents
- Administrator Responsibilities
- User Management
- System Configuration
- Data Management
- Security and Access Control
- Reporting and Analytics
- Maintenance and Troubleshooting
- Backup and Recovery
Administrator responsibilities
role of System Administrators
AllanaCrusis administrators (Manager role) are responsible for:
- User account management: Creating, modifying, and deactivating user accounts
- System configuration: Setting up organizational preferences and policies
- Data integrity: Ensuring accuracy and consistency of library data
- Security management: Controlling access and protecting sensitive information
- Performance monitoring: Maintaining system efficiency and reliability
- Training and support: Helping users understand and use the system effectively
access Level Requirements
Administrator functions require Manager role permissions:
- Full system access: All features and configurations
- User management: Create, edit, and delete user accounts
- System settings: Modify global configuration options
- Data management: Bulk operations and maintenance tools
- Security controls: Access to logs, permissions, and security settings
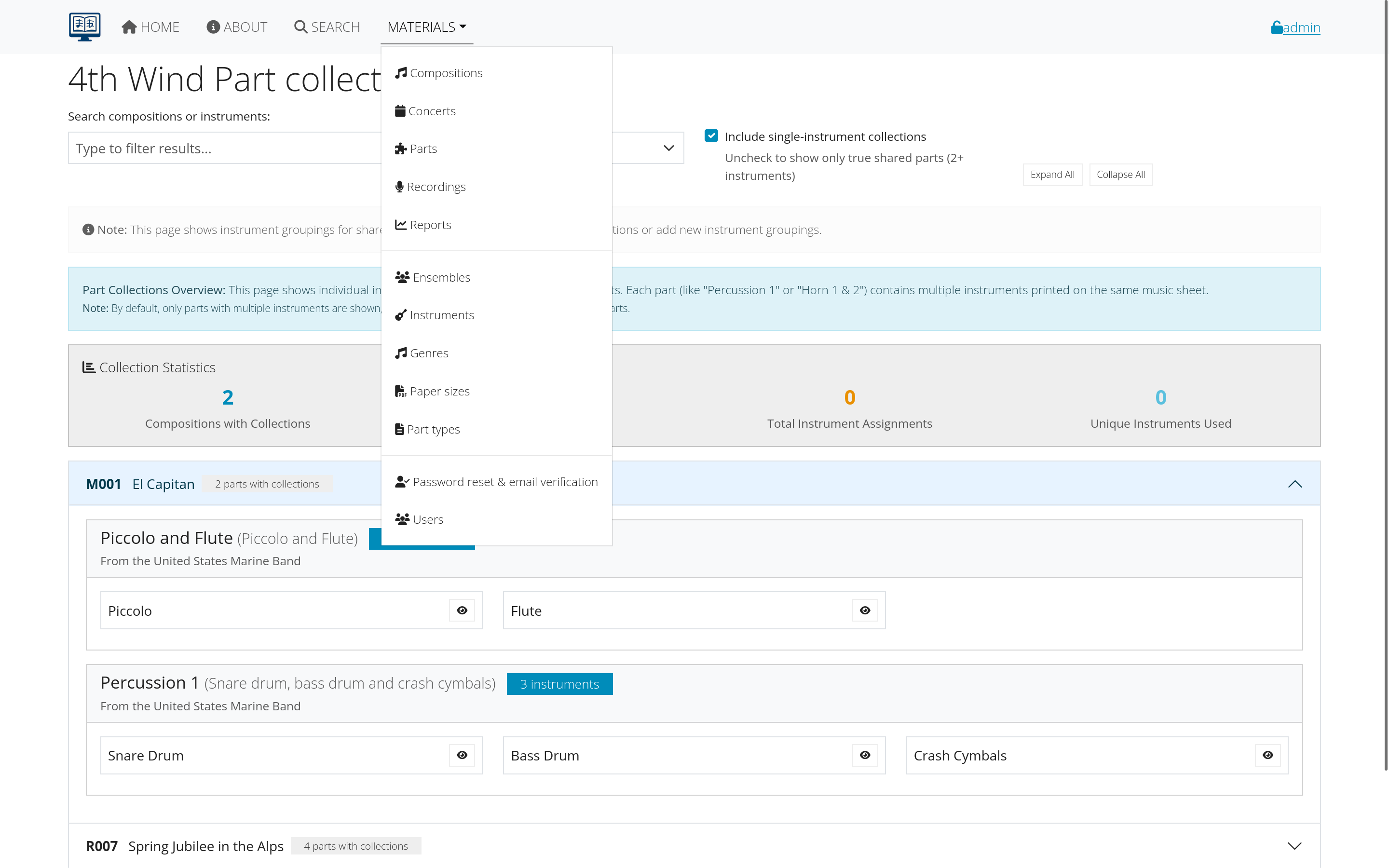 Figure 1: Administrator dashboard showing key management functions
Figure 1: Administrator dashboard showing key management functions
User management
user Account Administration
Accessing User Management:
- Navigate to ADMIN > Users
- View complete user list
- Search and filter users as needed
- Access individual user records
creating New User Accounts
Step-by-Step Process:
- Click “Add New User”
- Fill in required information:
- Username: Unique identifier
- Email address: Must be valid and unique
- Full name: First and last name
- Initial password: Temporary password for first login
- Role assignment: Guest, Member, Librarian, or Manager
- Ensemble assignment: Which group(s) user belongs to
- Set account options:
- Account status: Active, inactive, pending verification
- Email verification: Required or optional
- Password requirements: Force change on first login
- Expiration date: If account has time limit
- Save new account
- Notify user of account creation and login information
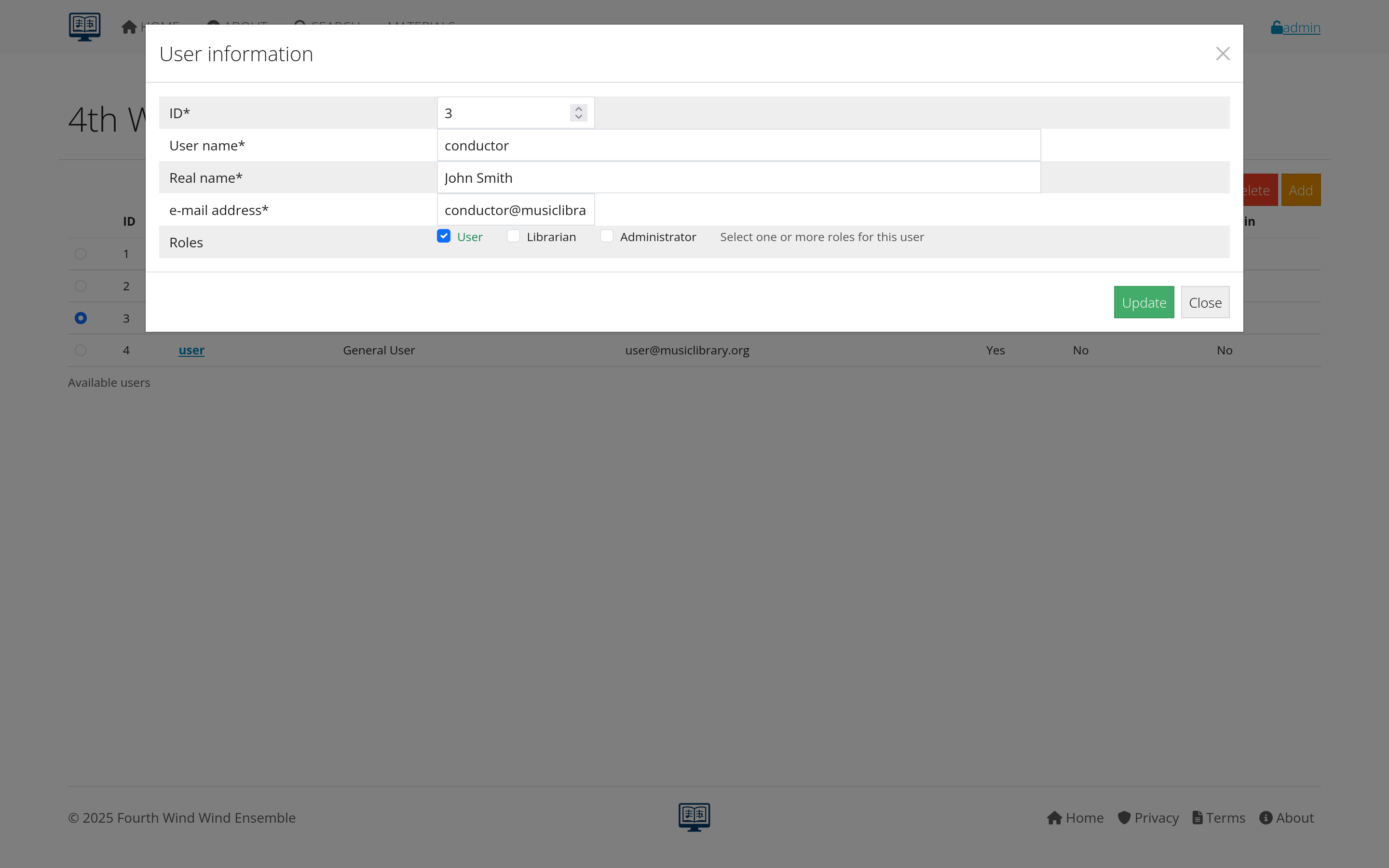 Figure 2: Form for creating new user accounts
Figure 2: Form for creating new user accounts
managing Existing Users
User Account Modifications:
- Role changes: Promote or demote user permissions
- Contact updates: Change email, name, or other details
- Password resets: Generate new passwords for locked accounts
- Account status: Activate, deactivate, or suspend accounts
- Ensemble assignments: Add or remove from groups
Bulk Operations:
- Mass role changes: Update multiple users simultaneously
- Ensemble transfers: Move groups of users between ensembles
- Account cleanup: Deactivate multiple inactive accounts
- Communication: Send messages to groups of users
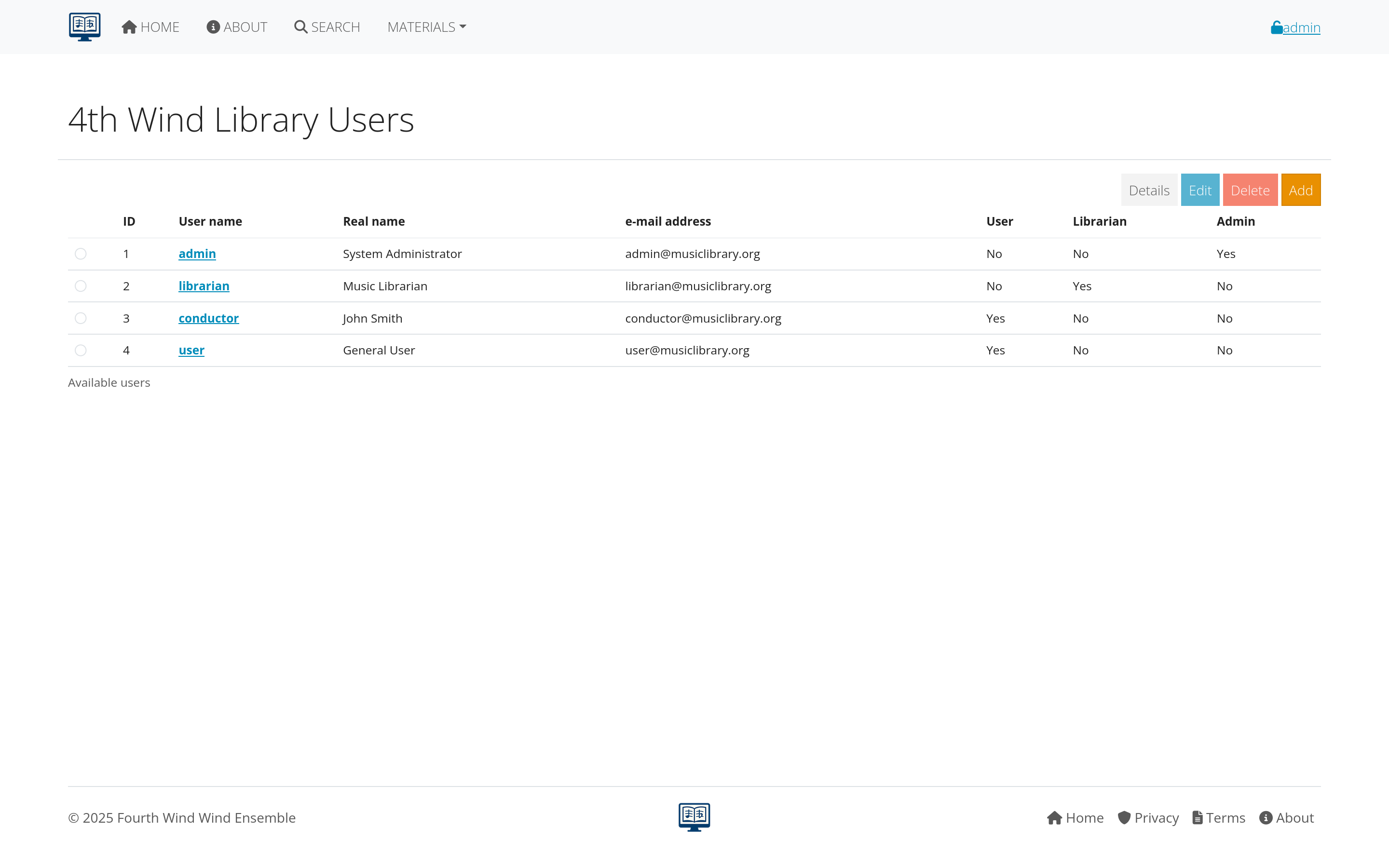 Figure 3: Interface for managing existing user accounts
Figure 3: Interface for managing existing user accounts
user Roles and Permissions
Role Hierarchy:
- Guest: Public access only, no login required
- Member: Basic authenticated access
- Librarian: Content management capabilities
- Manager: Full administrative control
Permission Matrix:
- Content viewing: All roles can view public content
- File downloads: Members and above (if configured)
- Content editing: Librarians and Managers only
- User management: Managers only
- System configuration: Managers only
Role Assignment Best Practices:
- Principle of least privilege: Give users minimum necessary access
- Regular review: Audit user roles periodically
- Documentation: Maintain records of why users have specific roles
- Change management: Process for requesting role changes
System configuration
global Settings
Organization Information:
- Library name: Display name for your organization
- Contact information: Administrative contact details
- Time zone: Default timezone for dates and times
- Language settings: Default language and localization
- Logo and branding: Customize appearance
System Behavior:
- Default permissions: New user and content defaults
- Email settings: SMTP configuration for system emails
- File upload limits: Maximum file sizes and formats
- Search configuration: Default search behavior and limits
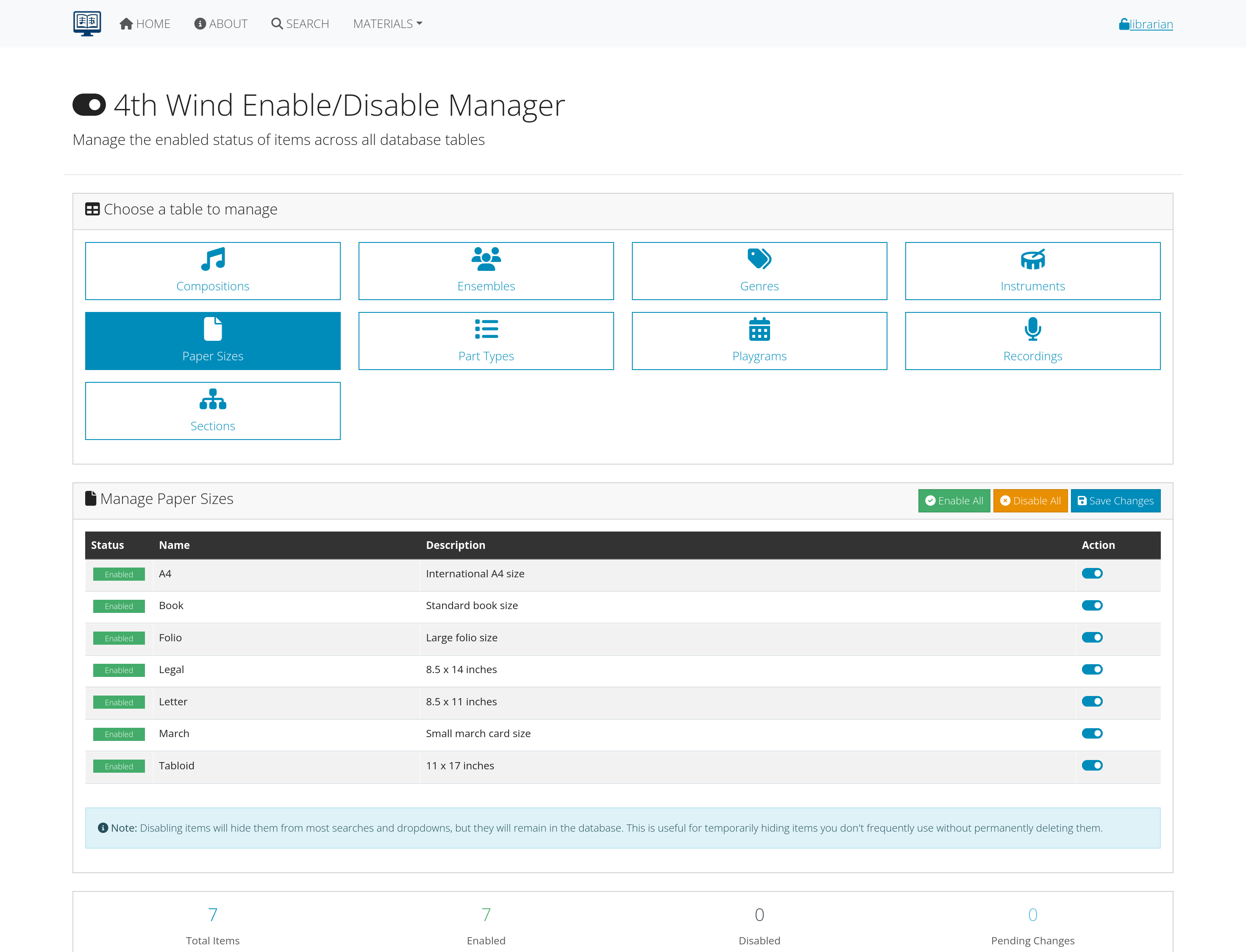 Figure 4: System configuration options and settings
Figure 4: System configuration options and settings
email Configuration
SMTP Settings:
- Mail server: Host and port configuration
- Authentication: Username and password for mail server
- Security: SSL/TLS encryption settings
- From address: Default sender for system emails
Email Templates:
- Welcome messages: New user account notifications
- Password resets: Automated password recovery
- Verification emails: Account activation messages
- System notifications: Updates and announcements
Testing and Validation:
- Test email functionality: Send test messages
- Monitor delivery: Check for bounced or failed emails
- Spam prevention: Configure to avoid spam filters
- Backup communication: Alternative contact methods
integration Settings
External Systems:
- Authentication integration: LDAP, Active Directory, SSO
- Calendar systems: Performance and event scheduling
- Website integration: Embedding AllanaCrusis content
- Third-party tools: Music software, databases, etc.
API Configuration:
- API access keys: For external system integration
- Rate limiting: Control API usage and prevent abuse
- Logging: Track API usage and troubleshoot issues
- Security: Authentication and authorization for API access
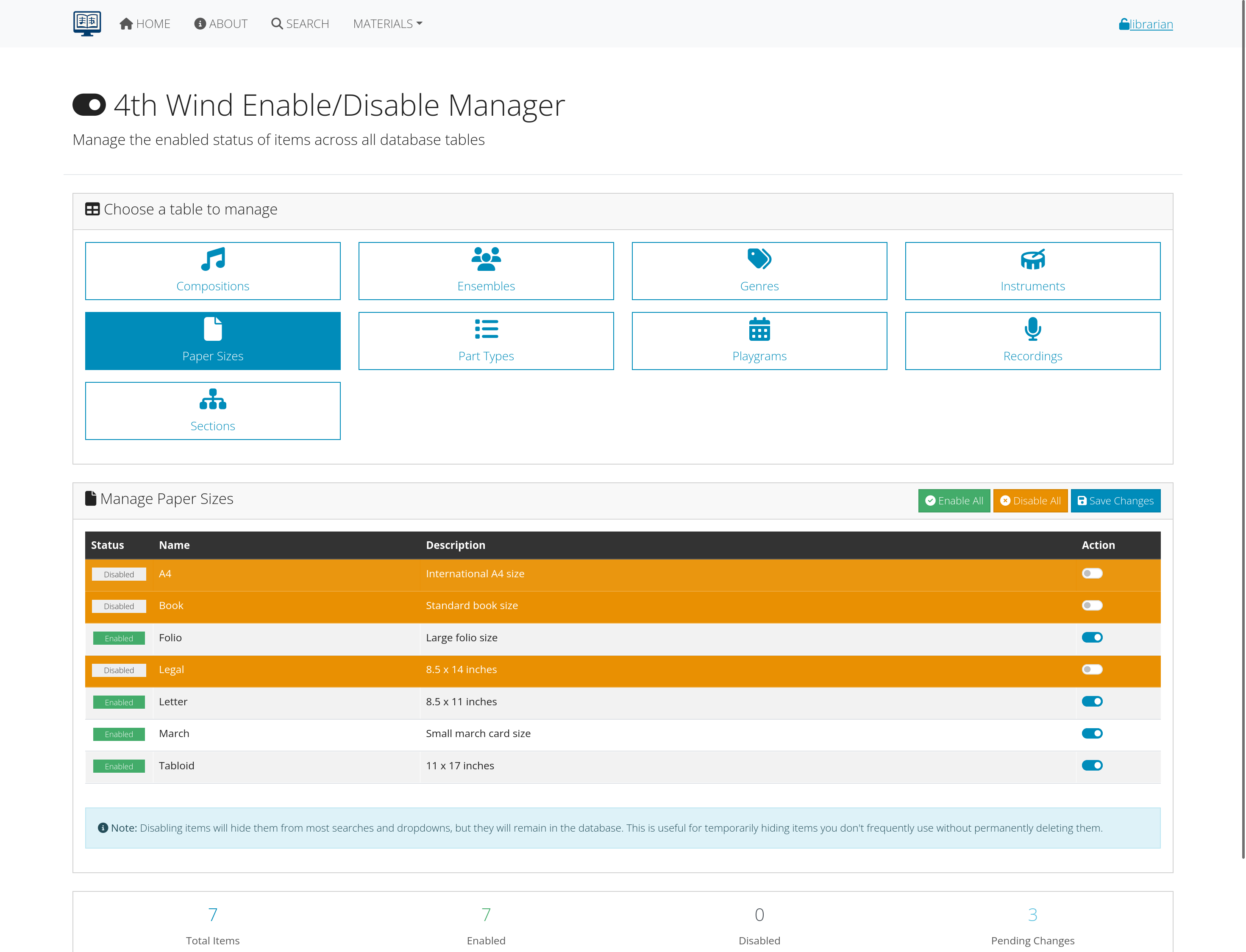 Figure 5: Configuration panel for external system integrations
Figure 5: Configuration panel for external system integrations
Data management
data Quality and Consistency
Regular Maintenance Tasks:
- Duplicate detection: Find and merge duplicate records
- Data validation: Check for missing or incorrect information
- Consistency checks: Ensure related records match properly
- Standardization: Apply naming and formatting conventions
Bulk Data Operations:
- Mass updates: Change multiple records simultaneously
- Data cleanup: Fix widespread data quality issues
- Migration tasks: Import data from other systems
- Archive management: Handle old or unused records
import and Export Functions
Data Import:
- CSV import: Bulk addition of compositions, parts, users
- Validation tools: Check data before importing
- Error reporting: Identify and fix import problems
- Progress tracking: Monitor large import operations
Data Export:
- Full database exports: Complete system backup
- Selective exports: Specific data sets or filtered results
- Report generation: Formatted outputs for analysis
- Scheduled exports: Automated regular backups
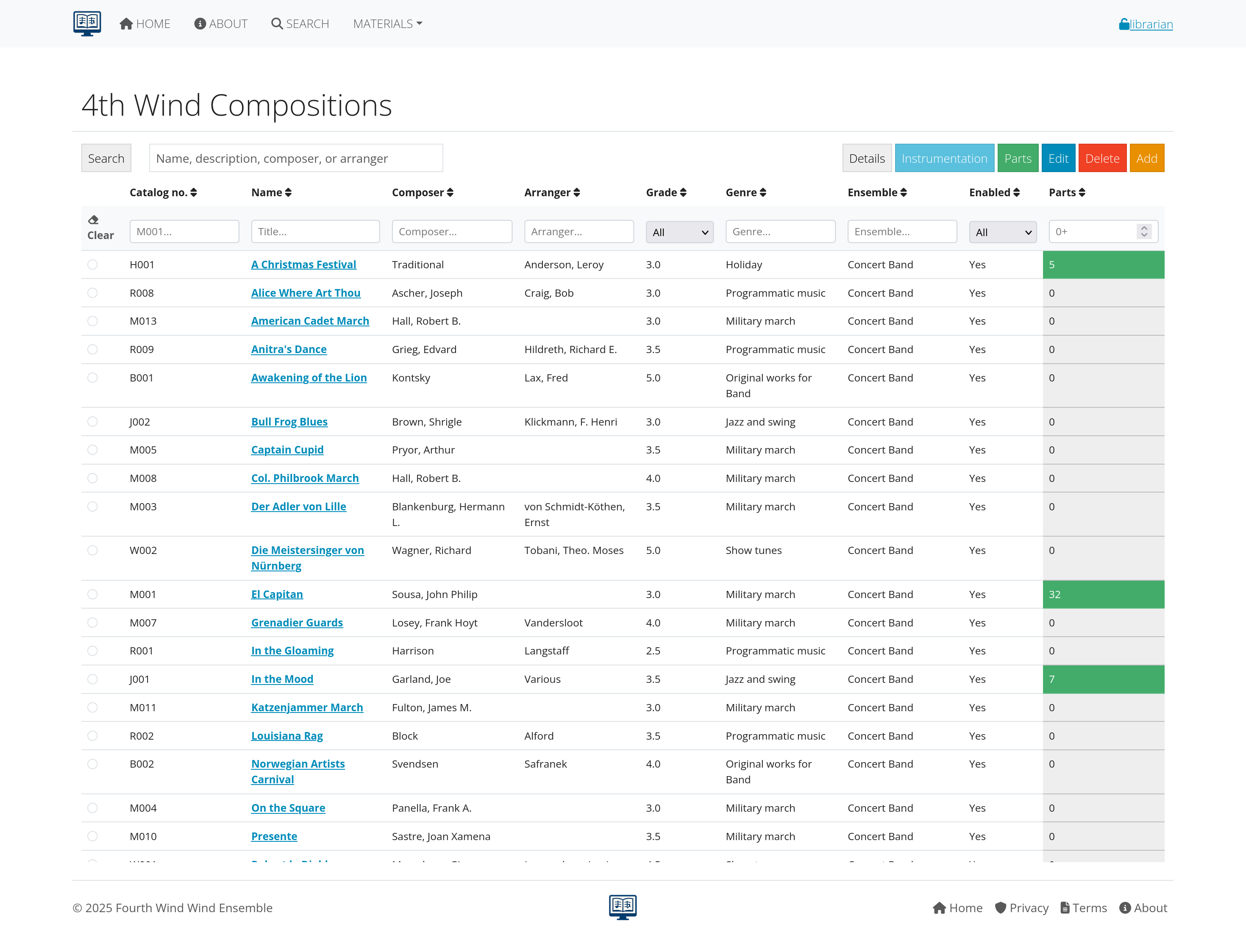 Figure 6: Tools for managing and maintaining data quality
Figure 6: Tools for managing and maintaining data quality
database Maintenance
Performance Optimization:
- Index management: Ensure efficient database queries
- Cache configuration: Speed up frequently accessed data
- Query optimization: Improve slow operations
- Storage management: Monitor disk usage and clean up
Integrity Checks:
- Referential integrity: Ensure related records connect properly
- Data validation: Check for corrupt or invalid data
- Backup verification: Confirm backups are working
- Recovery testing: Periodically test restoration procedures
Security and access control
security Policies
Access Management:
- Password policies: Requirements for user passwords
- Account lockout: Protection against brute force attacks
- Session management: Control how long users stay logged in
- Two-factor authentication: Additional security for sensitive accounts
Content Protection:
- Copyright compliance: Ensure proper licensing and permissions
- File access controls: Restrict access to authorized users
- Download monitoring: Track and limit file downloads
- Usage auditing: Monitor how materials are being used
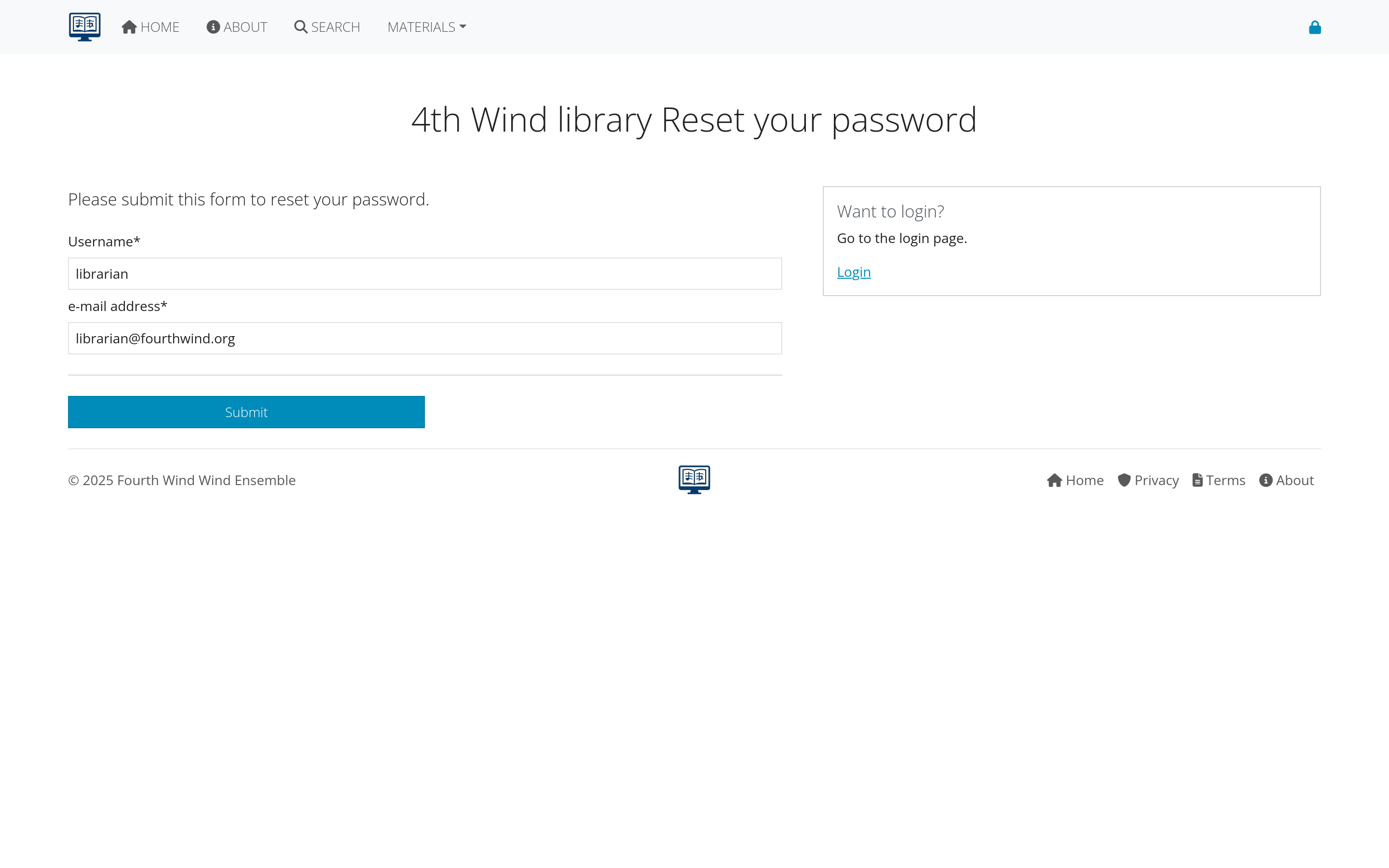 Figure 7: Security and access control configuration options
Figure 7: Security and access control configuration options
monitoring and Logging
System Logs:
- User activity: Login attempts, downloads, changes
- System events: Errors, performance issues, maintenance
- Security incidents: Unauthorized access attempts
- Data changes: Track modifications to important records
Log Analysis:
- Regular review: Check logs for unusual activity
- Automated alerts: Notification of security events
- Trend analysis: Identify patterns and potential issues
- Report generation: Summarize activity for management
backup and Security
Data Protection:
- Regular backups: Automated daily/weekly backups
- Offsite storage: Protect against local disasters
- Encryption: Secure backup files and transmissions
- Access controls: Limit who can access backup systems
Incident Response:
- Response procedures: Steps to take when problems occur
- Contact information: Who to notify in emergencies
- Recovery plans: How to restore service after problems
- Documentation: Record incidents and responses
Reporting and analytics
standard Reports
System Usage:
- User activity reports: Login frequency, feature usage
- Content access: Most popular compositions and parts
- Download statistics: File access patterns and trends
- Performance metrics: System speed and reliability
Library Analytics:
- Collection statistics: Size, growth, and composition of library
- Usage patterns: How different types of content are used
- User demographics: Analysis of user base and needs
- Trend analysis: Changes in usage over time
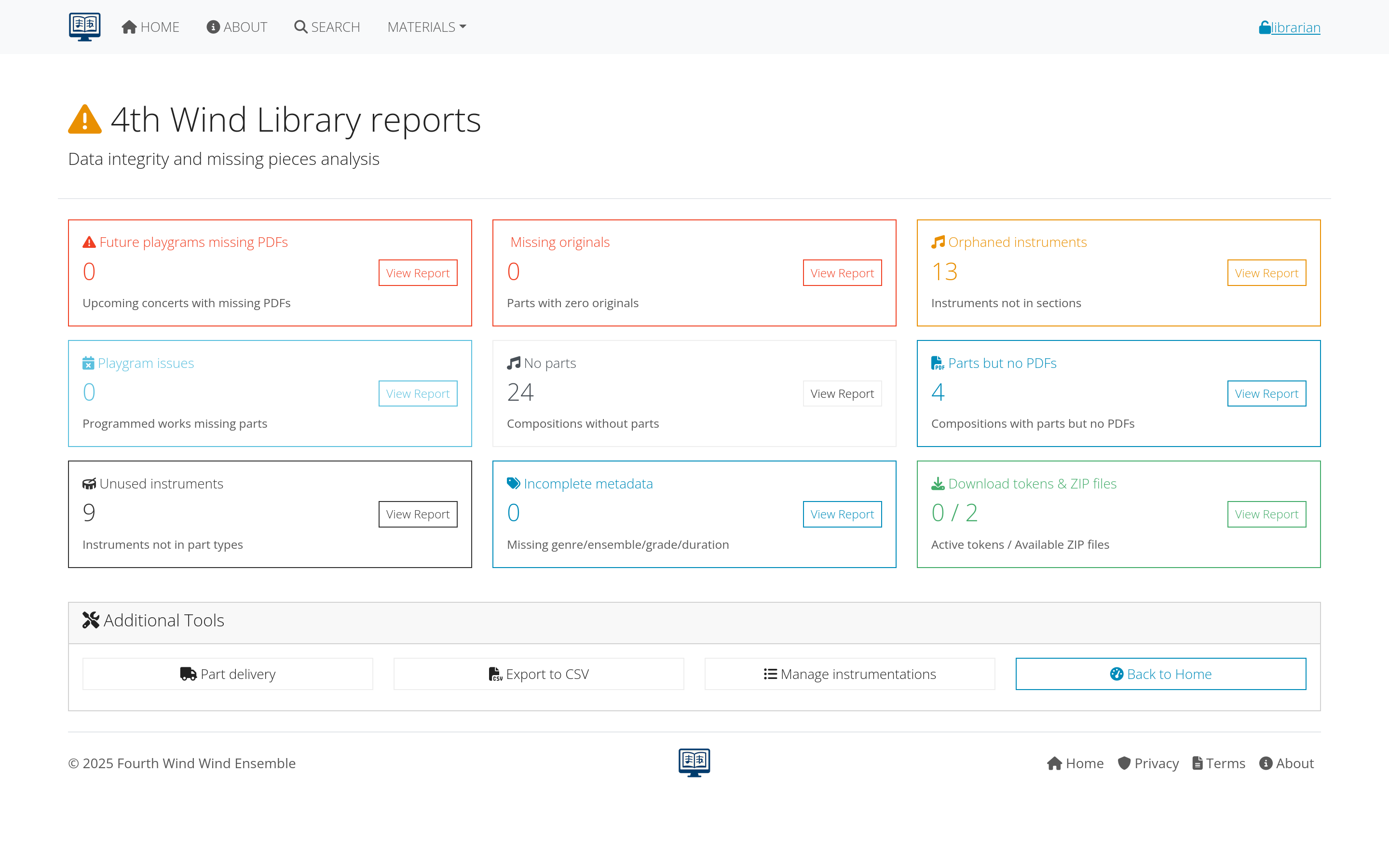 Figure 8: Comprehensive reporting and analytics dashboard
Figure 8: Comprehensive reporting and analytics dashboard
custom Reports
Report Builder:
- Field selection: Choose what data to include
- Filter criteria: Limit results to specific subsets
- Sorting options: Organize results meaningfully
- Output formats: PDF, CSV, web display options
Scheduled Reports:
- Automated generation: Regular reports without manual intervention
- Email delivery: Send reports to stakeholders automatically
- Archive management: Store historical reports for comparison
- Alert systems: Notify when metrics exceed thresholds
data Analysis Tools
Trend Analysis:
- Historical comparisons: How metrics change over time
- Seasonal patterns: Identify cyclical usage patterns
- Growth projections: Predict future needs and usage
- Performance benchmarks: Compare against organizational goals
User Behavior Analysis:
- Navigation patterns: How users move through the system
- Feature utilization: Which capabilities are used most
- Problem identification: Where users encounter difficulties
- Optimization opportunities: Ways to improve user experience
Maintenance and troubleshooting
system Maintenance
Regular Tasks:
- Software updates: Keep AllanaCrusis current with latest version
- Database optimization: Maintain performance and reliability
- File cleanup: Remove temporary and unnecessary files
- Security updates: Apply patches and security fixes
Scheduled Maintenance:
- Maintenance windows: Plan downtime for updates
- User notification: Inform users of scheduled maintenance
- Backup procedures: Ensure data protection during maintenance
- Testing protocols: Verify system functionality after maintenance
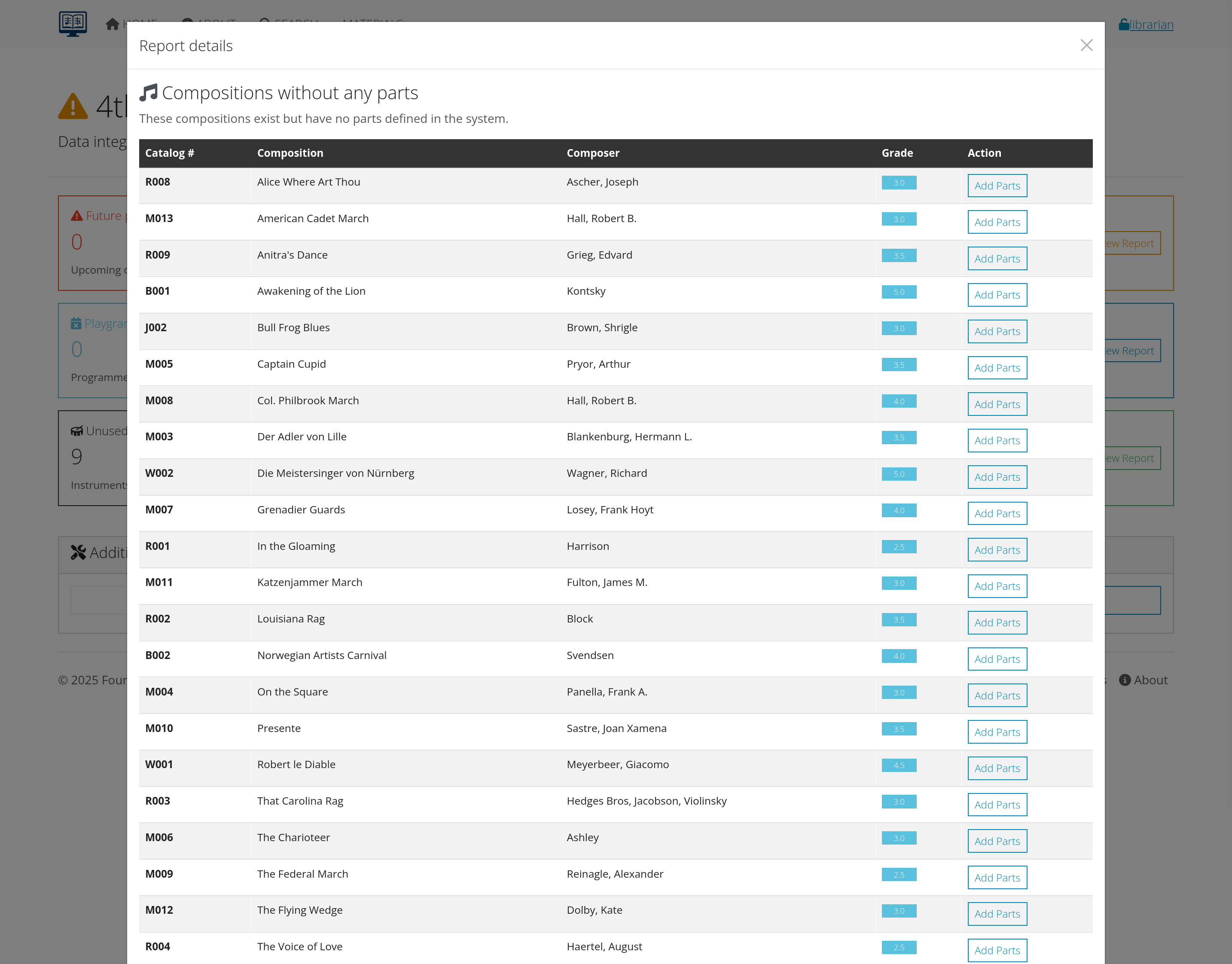 Figure 9: Interface for scheduling and managing system maintenance
Figure 9: Interface for scheduling and managing system maintenance
performance Monitoring
System Metrics:
- Response times: How quickly pages and features load
- Database performance: Query execution times and efficiency
- File download speeds: Network and storage performance
- Error rates: Frequency and types of system errors
Capacity Planning:
- Storage usage: Monitor disk space and plan expansion
- User load: Track concurrent users and system capacity
- Bandwidth utilization: Network usage and requirements
- Growth planning: Predict future hardware and software needs
troubleshooting Tools
Diagnostic Capabilities:
- System logs: Detailed error and activity information
- Performance profiling: Identify bottlenecks and slow operations
- Database analysis: Query performance and optimization
- User session tracking: Follow user interactions for problem diagnosis
Problem Resolution:
- Error documentation: Catalog common problems and solutions
- Escalation procedures: When and how to contact technical support
- Workaround strategies: Temporary solutions for ongoing issues
- Change management: Track fixes and their effectiveness
Backup and recovery
backup Strategy
Backup Types:
- Full backups: Complete system and data backup
- Incremental backups: Only changes since last backup
- Database backups: Specific backup of database content
- File backups: Uploaded files and digital content
Backup Schedule:
- Daily backups: Critical data backed up every day
- Weekly full backups: Complete system backup weekly
- Monthly archival: Long-term storage of complete backups
- Before updates: Special backups before system changes
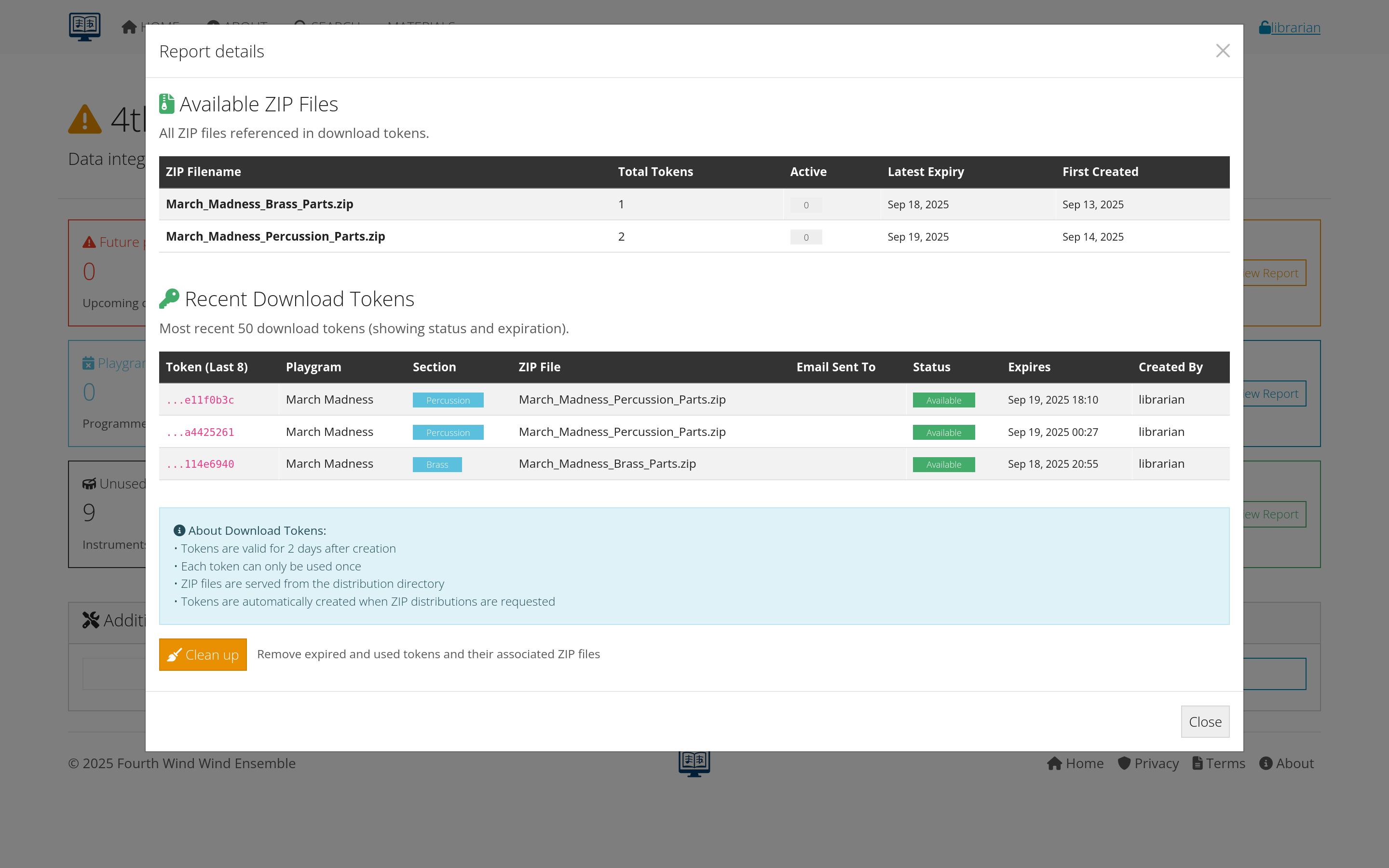 Figure 10: Backup and recovery management interface
Figure 10: Backup and recovery management interface
recovery Procedures
Recovery Planning:
- Recovery time objectives: How quickly system must be restored
- Recovery point objectives: How much data loss is acceptable
- Communication plans: How to notify users during outages
- Alternative access: Temporary solutions during recovery
Testing and Validation:
- Regular restore tests: Verify backups actually work
- Partial recovery: Test restoration of specific components
- Disaster scenarios: Plan for various types of failures
- Documentation: Maintain current recovery procedures
business Continuity
Contingency Planning:
- Alternative systems: Backup methods for critical functions
- Manual procedures: How to operate without the system
- Communication methods: Keep users informed during outages
- Priority restoration: Which functions to restore first
Risk Management:
- Risk assessment: Identify potential threats and vulnerabilities
- Mitigation strategies: Reduce likelihood and impact of problems
- Insurance considerations: Financial protection against major losses
- Vendor relationships: Support agreements and escalation procedures
Best practices for administrators
daily Operations
Routine Checks:
- Monitor system performance: Check for slowdowns or errors
- Review user activity: Look for unusual patterns or problems
- Check backup status: Ensure backups completed successfully
- Respond to user requests: Handle support tickets and questions
Proactive Management:
- User training: Ongoing education for effective system use
- Documentation maintenance: Keep procedures and policies current
- Security vigilance: Monitor for threats and vulnerabilities
- Continuous improvement: Regular evaluation and enhancement
long-term Strategy
Strategic Planning:
- Capacity planning: Anticipate growth and resource needs
- Technology roadmap: Plan for updates and new features
- User feedback: Incorporate user suggestions and needs
- Integration opportunities: Connect with other organizational systems
Change Management:
- Testing procedures: Validate changes before implementation
- User communication: Keep users informed of changes
- Training programs: Help users adapt to new features
- Rollback plans: Ability to reverse changes if problems occur
 Figure 11: Checklist of best practices for system administrators
Figure 11: Checklist of best practices for system administrators
Getting support
internal Resources
- User documentation: Complete guides for all system functions
- Training materials: Videos, tutorials, and reference guides
- User community: Other administrators and experienced users
- Organizational policies: Local procedures and guidelines
external Support
- Technical support: Developer or vendor assistance
- User forums: Community discussions and problem-solving
- Professional services: Consulting and implementation help
- Training providers: Formal education and certification
emergency Contacts
- System vendor: Primary technical support contact
- Hosting provider: Infrastructure and network support
- Internal IT: Organizational technical resources
- Management team: Escalation for business decisions
Next steps
As a system administrator:
- Review Troubleshooting Guide - Prepare for common issues
- Establish regular maintenance routines - Keep system running smoothly
- Plan for growth and changes - Anticipate organizational needs
- Build user support systems - Help users succeed with the system
Continue to the final section: Troubleshooting for comprehensive problem-solving guidance.